Server Certificate Model
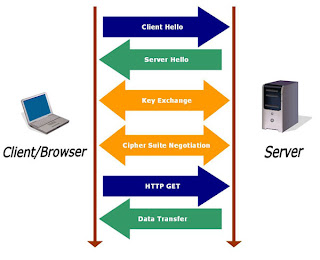
In this post we will discus a little about server certificate model. Yes you are right we will discus here something about CA certificates and SSL. So lets start from CA certificate. Full form of CA is certificate authority or certification authority its main task is to provide digital signatures which are known as CA certificates. The digital signatures/certificates certifies the ownership of a public key. There are several CA that provide digital certificates some are free while some are paid. The very common use of CA certificates can be found in SSL or TSL. The introduction of SSL in HTTP protocol has made possible data transfer via network in encrypted form. Due to introduction of SSL in HTTP the three way handshake is also slightly affected to support data transfer in encrypted form.
A digital certificate can be compared to a voter card id. A voter can be termed as a website, card issuing office as CA authorities and voter card number as secret cipher code. Cipher code for SSL is determined with help of cipher suite which is set of cryptographic primitives and configurations. It may include information about which key exchange algorithm to use, authentication algorithm, encryption, hashing and other information. SSL works on the basis of Public Key Infrastructure (PKI) and uses randomly generated session key for first time session key exchange with any website. The key exchange cycle involves setting up special session key that both client and server can use to communicate securely.
Now one of the biggest problem with SSL is that it only certifies that the certificate is issued to particular website for particular reason without any mechanism to verify it. That means you can use digital certificate verified for some other website for yourself. For most of the Windows ISS servers, these digital certificates and does not even needs real validation, it means if you activate HTTPS over HTTP in Windows ISS server then your SSL layer would be ready without any third party verification because it'll itself act as CA authority root server.
By the way the motive of this post was not explaining full working of SSL but to clear some basics that you must know to further understand our upcoming posts on attacking SSL encryption. So in upcoming posts we will have our look on SSL weaknesses and how to attack them. Till then thanks for reading, have a nice time and keep visiting.