In following tutorial we will cover how to use DarkComet Remote Administration Tool. If you regular reader to Devil's Blog then you might be knowing we have already covered Cerberus RAT client in The RAT Remote Administration Tool then why we are covering another RAT client.
Following are 4 good reasons for that.
1.Many people think that DarkComet is best RAT client and they don't prefer any other RAT client than DarkComet.(not my personal view)
2.Few days ago we covered Denial Of Service and Types Of DoS Attacks soon we will cover tools that can be used for DoS attack and DarkComet is one of those tools that can be used for launching a successful DDoS attack. 3.Search engines are dropping visitors searching for Dark Comet tutorial on Cerberus tutorial, not good na, better give them what they are searching for.
4.Its always better if you know how to handle more than one tool.
Enough talk lets move on to tutorial. Download DarkComet RAT 2.2 from their official website. You might ask why 2.2 when 3.2 is available. 3.2 is unstable and needs some bug fixes better opt 2.2. After download extract zip file and double click on RAT client, accept EULA and you will be presented with following screen.
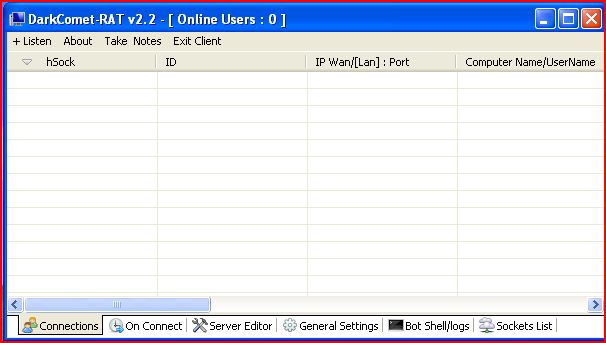 |
| Main Window |
Now click on edit server.
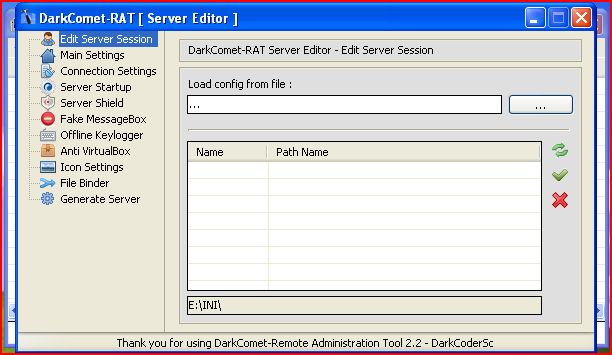 |
| Server Editor |
Server Session:
If you have already created any RAT server before then Darkcomet stores an INI file with all settings saved in it. So if you want to create another server with same settings open that file here and create server.
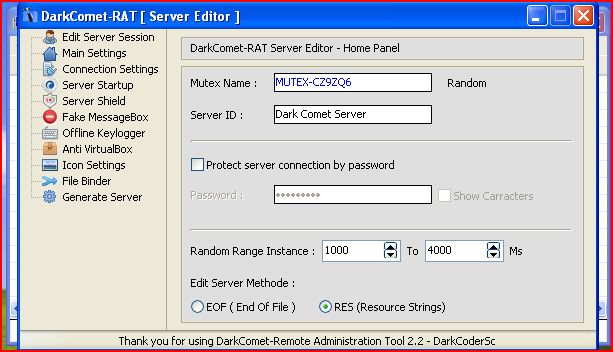 |
| Main Settings |
Mutex String:
Our RAT client will run in process space of another process to remain stealthy. This string helps differentiate RAT that some another process is holding our data for hiding. Must be specified for proper functioning of RAT client, you can give it any name you want or just press random to get random name.
Server ID:
This name will appear on server list when your victim will execute your server. Helps in differentiating different servers so better use new name for new server.
Lastly always preserve connection with good user-name and password.
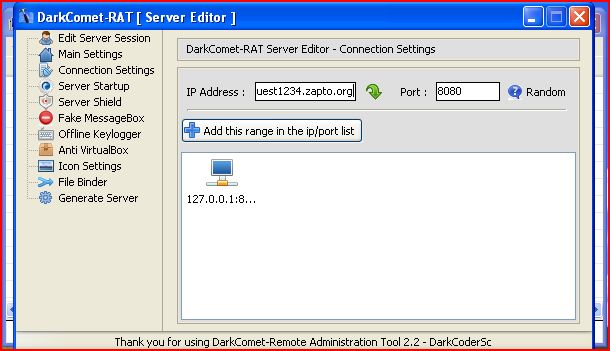 |
| Connection Settings |
Specify your IP address in IP address field if you have static IP or use Dynamic DNS if your IP address is not static. To know more about Dynamic DNS IP read Use Dynamic IP As Static IP. Now specify port number you want to listen and press “Add This Range In IP/port list”. For testing purpose you can use 127.0.0.1 that is loop back IP and port 8080 I.e http proxy port.
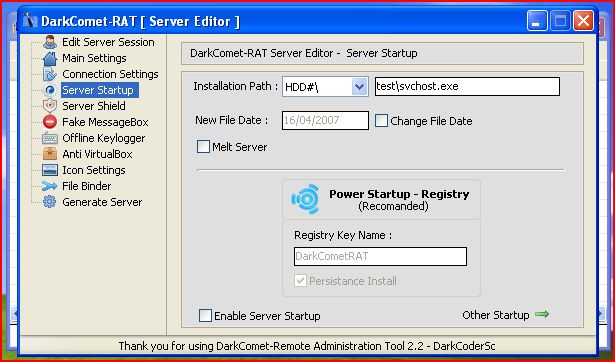 |
| Server Startup |
Here you can specify where your sever will get installed in victim's PC and you can also specify in which process you wish to hide you server. A good choice for process is svchost.exe, melt server option will delete server file as soon as server gets installed. Other options includes adding registry keys, use them if you want but it works fine without any key. Don't forget to enable option of “Start Server ON Startup”.
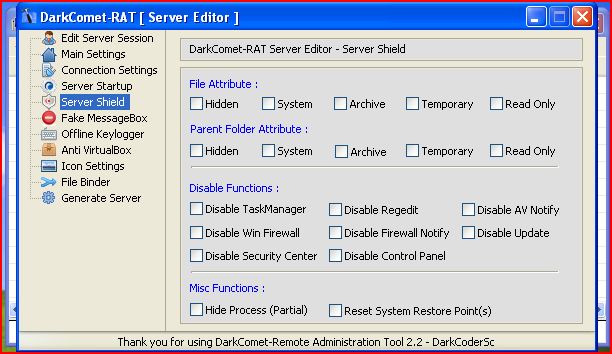 |
| Server Shield |
Server Shield provides server with file attributes and folder attributes for installation and basic fun options to harass victim. I would better advise not to use them because it will alarm user about presence of your RAT server.
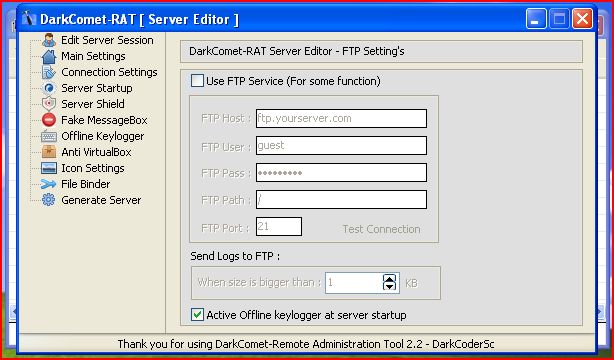 |
| Offline Key Logger |
Activate offline key-logger so that key-logger should log files even though you are offline. If you want server to send log files to your ftp server rather than accumulating in victim PC, specify credentials required for your ftp server. If you don't have ftp server, you can search for “free ftp service” on Google and you will get heap of them or you can try out http://www.zymic.com/free-web-hosting/ it offers free-web-hosting plus free ftp service. Good for practice.
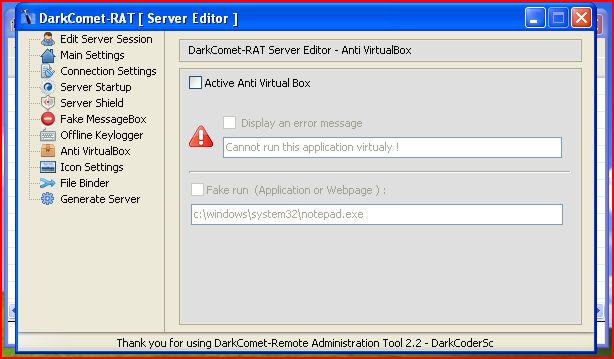 |
| Anti VirtualBox |
Anti Virtual Box settings allow RAT client to disallow server execution in virtual environment. But since you will be practicing it in virtual environment don't touch this option. To know how to setup your virtual lab read Basic Lab Setup For Hacker. Next is icon setting use some good custom icon so that your victim should not feel suspicious about RAT server.
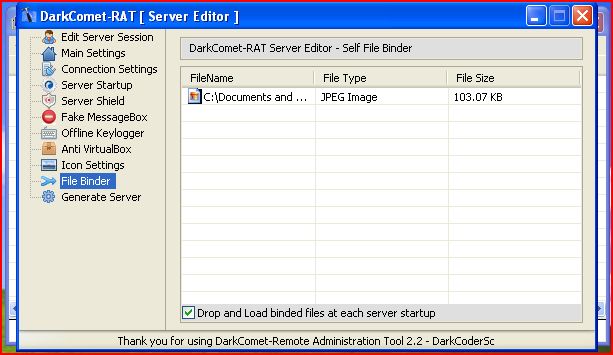 |
| File Binder |
Select file you want to bind with RAT server, binding with another file make RAT server remain in stealth mode and get executed with legitimate file thus avoiding detection.
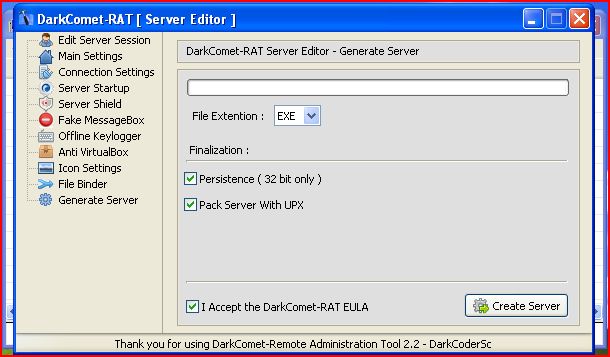 |
| Generate Server |
Now select all options and generate server.
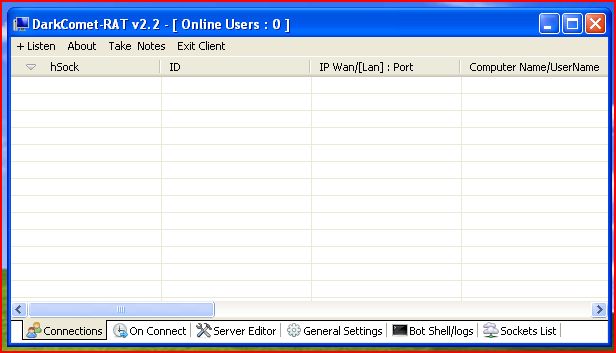 |
| Listen |
Now close server edit window and press listen, specify port number 8080 and then execute your RAT server.
 |
| Listening On Port 8080 |
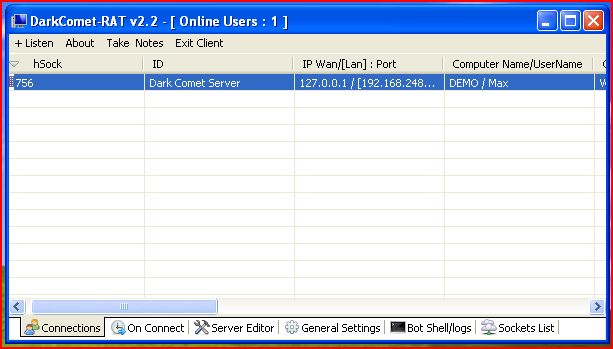
Now right click on listening port and select “Open Control Center”, play with available options.
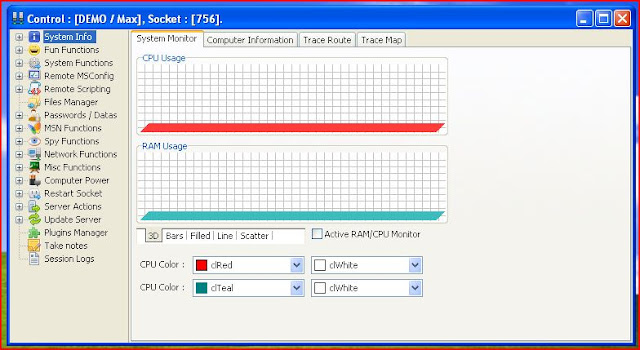 |
| Control Center |
Actually you are not in need of any remote PC to practice, if you have set your virtual environment then follow above steps in virtual environment with IP address 127.0.0.1 and port number 8080, if your firewall shouts ask it to allow connection. With this setting you will not even need internet connection to see results while practicing. This will help those who have computers at home but for Internet connection they have to depend on college, schools and cafes. Please ask if you have any difficulty or query. Thanks for reading, keep visiting.